Overview
At Ferrara IT, we deliver fully integrated Managed IT and Managed cybersecurity solutions as a Managed Services Provider (MSP) and Managed Security Services Provider (MSSP). Our security-first approach combines advanced tools, proactive threat detection, rapid incident response, and compliance-focused risk assessments—designed to protect your business, reduce risk, and keep you audit-ready.
Based just outside Philadelphia, Ferrara IT proudly supports clients nationwide—bringing our expertise to law firms, healthcare organizations, financial institutions, nonprofits, and other compliance-heavy industries.
With Ferrara IT, you get a single trusted partner for all your IT, security, and compliance needs.
approach
Our multilayered cybersecurity framework ensures end-to-end protection, covering everything from endpoint security to advanced threat detection and response. Each layer reinforces the next, creating a robust security posture that safeguards your business from evolving threats.
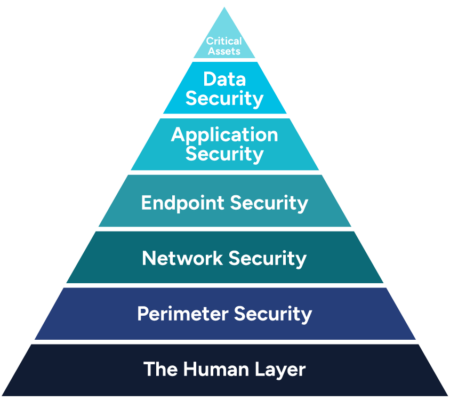
People are your first line of defense—and often your weakest link. Our on-going employee security training, simulated phishing tests, and AI email filtering empower your team to detect and block threats.
We utilize next-gen firewalls and intrusion prevention systems that block unauthorized access, malware, and DDoS attacks. Secure remote access and network segmentation further ensure employees access only what they need while isolating critical systems to limit internal threats.
Once inside your network, attackers try to move laterally, but our 24/7 SOC, SIEM analysis, and MDR services stop them before they reach critical systems. We continuously monitor and analyze activity to detect and neutralize threats before they escalate.
Every laptop, desktop, mobile device, and BYOD is a potential gateway for cyberattacks. Our AI-driven endpoint detection and automated patch management work together to secure every device in real time.
Your cloud apps (Microsoft 365, Azure, AWS, and SaaS) require robust security to prevent unauthorized access and data breaches. We use continuous cloud posture management to fix vulnerabilities, enforce MFA and identity protection, and monitor the dark web for compromised credentials.
We protect your data from leaks, ransomware, and compliance violations. We combine Data Loss Prevention to block unauthorized sharing, ransomware protection with immutable backups for rapid recovery, and encryption with role-based access controls to ensure only authorized access.
overview
Security Solutions
Enhance your security posture with our comprehensive suite of threat detection and response services:
• Endpoint Detection & Response (EDR): Advanced threat protection for endpoints with real-time monitoring and immediate response.
• MDR & XDR: 24/7 expert-driven security monitoring, incident response, and proactive threat hunting that consolidates data across endpoints, networks, and cloud environments for a holistic defense.
• 24/7 Security Operations Center (SOC): A dedicated, round-the-clock operations center that continuously monitors, identifies, and coordinates rapid incident response to emerging threats.
• Security Information & Event Management (SIEM): Centralized log management, real-time threat detection, and compliance reporting. Read our blog: Why every company needs MDR and SIEM and how they work together


Security Solutions
Ensure only the right individuals gain secure access to your critical resources.
• Privileged Access Management (PAM): Secure control over administrative accounts using least privileged, just-in-time access to prevent unauthorized access.
• Identity & Access Management (IAM): Streamlined user authentication, authorization, and identity governance.
• Zero Trust Security: Continuous verification of users and devices to eliminate implicit trust.
• Single Sign-On (SSO) & Multi-Factor Authentication (MFA): Enhanced authentication security across all enterprise systems. Read our blog: The importance of enforcing MFA
Security Solutions
Strengthen your digital defenses with our comprehensive network and endpoint protection solutions:
• Firewall Management & Intrusion Prevention (IDS/IPS):
Defend your network from unauthorized access and cyber threats.
• Patch & Vulnerability Management:
Keep your systems up to date and secure against known exploits.
• Data Loss Prevention (DLP):
Safeguard sensitive information by preventing unauthorized data access and leakage.
• Email Security & Anti-Phishing Protection:
Shield your organization from phishing attacks, business email compromise, and malware.


Security Solutions
Protect your digital environment with our advanced cloud and infrastructure security solutions designed to enforce best practices, control data access, and mitigate cyber risks.
• Cloud Security Posture Management (CSPM): Enforce security best practices across Azure, AWS, and Google Cloud.
• Cloud Access Security Broker (CASB): Control data security and manage access across cloud applications.
• Microsegmentation & Network Segmentation: Isolate critical systems to minimize the impact of cyber attacks.
• Workload & Container Security: Protect virtual machines, containers, and cloud-native applications.
Our Process
Every business has unique security needs. Whether you’re just starting to build a cybersecurity strategy or need fully managed protection, Ferrara IT can help.

Get a customized security recommendation roadmap that aligns with your business objectives and risk profile.

Get expert implementation of advanced security solutions to protect your business.

Rely on our team for on-going 24/7 threat monitoring, rapid incident response, and continuous protection.
Assessments
As cyberattacks continue to rise, identifying your security gaps is crucial for protecting your business. Our comprehensive IT assessments uncover vulnerabilities, inefficiencies, and compliance gaps before they turn into costly problems, and in addition to the assessments listed below, we offer many others.
Uncover risks within Microsoft 365 and Azure AD. Obtain a risk score and actionable recommendations based on Microsoft best practices.
Schedule Cloud AssessmentAnalyze on-premise Active Directory and LAN for misconfigurations and best practice violations. Reports provides actionable solutions.
Schedule Network AssessmentIdentify hidden vulnerabilities that could be exploited by a successful phishing attack or attackers who has managed to breach your firewall.
Schedule Cyber AssessmentSimulate real-world cyberattacks to uncover vulnerabilities in networks, cloud and applications. Strenghten security, and reduce risk.
Schedule Penetration TestingNot sure which assessment is right for you? Explore our full range of risk assessments to identify security gaps and protect your business.
Benefits
One vendor, one solution—get expert IT support, advanced cybersecurity, and compliance help from a single trusted partner.
Our security team monitors and responds to threats in real time using a powerful stack: EDR, XDR, SIEM, and MDR.
We help you meet HIPAA, FINRA, GLBA, PCI-DSS, and NIST standards—without the confusion or compliance fatigue.
From endpoint hardening to user training and vulnerability scans, we reduce your risk from every angle.
Stay operational with secure backups, disaster recovery planning, and expert-led incident response when it matters most.
Let’s strengthen your security today. Let’s get started

Customer Testimonial
“We used to struggle with malware and security breaches, but Ferrara IT implemented advanced security solutions that changed everything. They continuously bring us the latest technology to keep our business protected and conduct regular employee security training to ensure our team remains vigilant against cyber threats.”
Non-Profit Organization
We know there are many IT companies out there, but at Ferrara IT, we do things differently. With a strategic, honest, and security-first approach, we prioritize your business needs and long-term success. Schedule a call and see the difference for yourself.

Let’s talk! We’ll discuss your IT challenges, business goals, and security needs to understand how we can help.
Our experts will evaluate your IT environment and provide recommendations for optimization.
Typically within just one week, we will provide a custom IT strategy and solutions proposal designed to align with your business goals.
Let’s Find the Right IT Solution for You.
Tell us what you need, and our team will reach out within one business day.